Received a couple of recent questions around SMB encryption, which is supported in addition to the other components of the SMB3 protocol dialect that OneFS supports, including multi-channel, continuous availability (CA), and witness.
OneFS allows encryption for SMB3 clients to be configured on a per share, zone, or cluster-wide basis. When configuring encryption at the cluster-wide level, OneFS provides the option to also allow unencrypted connections for older, non-SMB3 clients.
The following CLI command will indicate whether SMB3 encryption has already been configured globally on the cluster:
# isi smb settings global view | grep -i encryption Support Smb3 Encryption: No
The following table lists what behavior a variety of Microsoft Windows and Apple Mac OS versions will support with respect to SMB3 encryption:
| Operating System | Description |
| Windows Vista/Server 2008 | Can only access non-encrypted shares if cluster is configured to allow non-encrypted connections |
| Windows 7/Server 2008 R2 | Can only access non-encrypted shares if cluster is configured to
allow non-encrypted connections |
| Windows 8/Server 2012 | Can access encrypted share (and non-encrypted shares if cluster is configured to allow non-encrypted connections) |
| Windows 8.1/Server 2012 R2 | Can access encrypted share (and non-encrypted shares if cluster is configured to allow non-encrypted connections) |
| Windows 10/Server 2016 | Can access encrypted share (and non-encrypted shares if cluster is configured to allow non-encrypted connections) |
| OSX10.12 | Can access encrypted share (and non-encrypted shares if cluster is configured to allow non-encrypted connections) |
Note that only operating systems which support SMB3 encryption can work with encrypted shares. These operating systems can also work with unencrypted shares, but only if the cluster is configured to allow non-encrypted connections. Other operating systems can access non-encrypted shares only if the cluster is configured to allow non-encrypted connections.
If encryption is enabled for an existing share or zone, and if the cluster is set to only allow encrypted connections, only Windows 8/Server 2012 and later and OSX 10.12 will be able to access that share or zone. Encryption cannot be turned on or off at the client level.
The following CLI procedures will configure SMB3 encryption on a specific share, rather than globally across the cluster:
As a prerequisite, ensure that the cluster and clients are bound and connected to the desired Active Directory domain (for example in this case, ad1.com).
To create a share with SMB3 encryption enabled from the CLI:
# mkdir -p /ifs/smb/data_encrypt # chmod +a group "AD1\\Domain Users" allow generic_all /ifs/smb/data_encrypt # isi smb shares create DataEncrypt /ifs/smb/data_encrypt --smb3-encryption-enabled true # isi smb shares permission modify DataEncrypt --wellknown Everyone -d allow -p full
To verify that an SMB3 client session is actually being encrypted, launch a remote desktop protocol (RDP) session to the Windows client, log in as administrator, and perform the following:
- Ensure a packet capture and analysis tool such as Wireshark is installed.
- Start Wireshark capture using the capture filter “port 445”
- Map the DataEncrypt share from the second node in the cluster
- Create a file on the desktop on the client (eg. README-W10.txt).
- Copy the README-W10.txt file from the Desktop on the client to the DataEncrypt shares using Windows explorer.exe
- Stop the Wireshark capture
- Set the Wireshark the display filter to “smb2 and ip.addr for node 1
- Examine the SMB2_NEGOTIATE packet exchange to verify the capabilities, negotiated contexts and protocol dialect (3.1.1)
- Examine the SMB2_TREE_CONNECT to verify the that encryption support has not been enabled for this share
- Examine the SMB2_WRITE requests to ensure that the file contents are readable.
- Set the Wireshark the display filter to “smb2 and ip.addr for node 2
- Examine the SMB2_NEGOTIATE packet exchange to verify the capabilities, negotiated contexts and protocol dialect (3.1.1)
- Examine the SMB2_TREE_CONNECT to verify the that encryption support has been enabled for this share
- Examine the communication following the successful SMB2_TREE_CONNECT response that the packets are encrypted
- : Save the Wireshark Capture to the DataEncrypt share using the name Win10-SMB3EncryptionDemo.pcap.
SMB3 encryption can also be applied globally to a cluster. This will mean that all the SMB communication with the cluster will be encrypted, not just with individual shares. SMB clients that don’t support SMB3 encryption will only be able to connect to the cluster so long as it is configured to allow non-encrypted connections. The following table presents the available global SMB3 encryption config options:
| Setting | Description |
| Disabled | Encryption for SMBv3 clients in not enabled on this cluster. |
| Enable SMB3 encryption | Permits encrypted SMBv3 client connections to Isilon clusters, but does not make encryption mandatory. Unencrypted SMBv3 clients can still connect to the cluster when this option is enabled. Note that this setting does not actively enable SMBv3 encryption: To encrypt SMBv3 client connections to the cluster, you must first select this option and then activate encryption on the client side. This setting applies to all shares in the cluster.
|
| Reject unencrypted SMB3 client connections | Makes encryption mandatory for all SMBv3 client connections to the cluster. When this setting is active, only encrypted SMBv3 clients can connect to the cluster. SMBv3 clients that do not have encryption enabled are denied access. This setting applies to all shares in the cluster. |
The following CLI syntax will configure global SMB3 encryption:
# isi smb settings global modify --support-smb3-encryption=yes
Verify the global encryption settings on a cluster by running:
# isi smb settings global view | grep -i encrypt Reject Unencrypted Access: Yes Support Smb3 Encryption: Yes
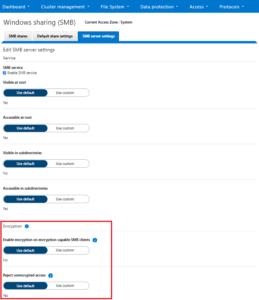
Global SMB3 encryption can also be enabled from the WebUI by browsing to Protocols > Windows Sharing (SMB) > SMB Server Settings: