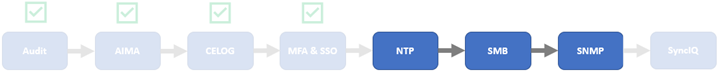
As mentioned in previous articles in this series, applying a hardening profile is one of multiple tasks that are required in order to configure a STIG-compliant PowerScale cluster. These include:
| Component | Tasks |
| Audit | Configure remote syslog servers for auditing. |
| Authentication | Configure secure auth provider, SecurityAdmin account, and default restricted shell. |
| CELOG | Create event channel for security officers and system admin to monitor /root and /var partition usage, audit service, security verification, and account creation. |
| MFA & SSO | Enable and configure multi-factor authentication and single sign-on. |
| NTP | Configure secure NTP servers with SHA256 keys. |
| SMB | Configure SMB global settings and defaults.
Enable SMB encryption on shares. |
| SNMP | Enable SNMP and configure SNMPv3 settings. |
| SyncIQ | Configure SyncIQ to use CA certificates so both the source and target clusters (primary and secondary DSCs) have both Server Authentication and Client Authentication set in their Extended Key Usages fields. |
In this article, we’ll cover the specific configuration requirements and details of the NTP, SMB, SNMP components using the OneFS CLI.
NTP Setup

- When implementing a secure configuration for the OneFS NTP service, create an NTP key file and populate it with NTP server key hashes.
To add secure NTP servers to the OneFS configuration, first create an NTP keys file. This can be accomplished via the following CLI syntax:
# echo "[key index] sha256 [SHA hash]" > [keyfile]
Where:
| Item | Description |
| [key index] | The index (increasing from 1) of the key hash. |
| [SHA hash] | The SHA256 hash identifying the NTP server. |
| [keyfile] | The path to the NTP key file. |
Append as many additional key entries as are necessary. The ntp.keys(5) man page provides detailed information on the NTP key file format.
- Next, configure OneFS to use this NTP key file.
# isi ntp settings modify --key-file /ifs/ntp.keys
- The following CLI syntax can be used to configure NTP servers.
# isi ntp servers create [server hostname/IP] --key [key index]
Where:
| Item | Description |
| [server hostname/IP] | The fully qualified domain name (FQDN) or IP address of the NTP server. |
| [key index] | The key used by this particular server in the NTP keys file configured above.. |
Note that STIG requirements explicitly state that more than one (1) NTP server is required for compliance.
SMB setup

- Deploying SMB in a hardened environment typically involves enabling SMB3 encryption, security signatures, and disabling unencrypted access to shares. To accomplish this, first configure the global settings and defaults as follows.
# isi smb settings global modify --support-smb3-encryption true --enable-security-signatures true --require-security-signatures true --reject-unencrypted-access true # isi_gconfig registry.Services.lwio.Parameters.Drivers.srv.SupportSmb1=0 # isi_gconfig registry.Services.lwio.Parameters.Drivers.rdr.Smb1Enabled=0
- Next, update the per-share SMB settings to enable SMB encryption.
# isi smb shares modify [share_name] --smb3-encryption-enabled true
SNMP Setup

- The following CLI command can be used to enable the OneFS SNMP v3 service and configure its settings and password.
# isi snmp settings modify --service=true --snmp-v3-access=true --snmp-v3-password=[password]
In the next and final article in this series, we’ll focus on the remaining topic in the list:

Namely secure SyncIQ configuration.